Why Hack the Election, When You Can Just Hack the Reporting?
 Republican nominee Donald Trump has been alleging for weeks that the election will be rigged, though many have pointed out that the election is far too decentralized to game. By contrast, the Associated Press (AP) provides a single, consolidated, and potentially very vulnerable target to anyone wishing to wreak havoc on Nov. 8.
Republican nominee Donald Trump has been alleging for weeks that the election will be rigged, though many have pointed out that the election is far too decentralized to game. By contrast, the Associated Press (AP) provides a single, consolidated, and potentially very vulnerable target to anyone wishing to wreak havoc on Nov. 8.
On election night, cable news networks and news sites rely on the AP for prompt, accurate totals as they come in from voting precincts across the country. Politico reported last week that “multiple sources in media, government and the security industry fretted about the effect if the AP were to get hit, and what that would do to their ability to get the news out.”
Sean Sullivan, a security adviser with cybersecurity firm F-Secure, explained on Wednesday just how at risk AP’s systems might be.
In a blog post entitled, “Hacking An Election Is Hard. Why Not Pwn The Messenger Instead?” Sullivan describes how he used his company’s proprietary tool for crawling site metadata and uncovered what appeared to be a legacy server from 2006 called “apvotecount2” as well as a more current one from 2010 called “apvotecount.”
On an FAQ page that explains how votes are reported and counted, the AP describes an “election night system” that receives vote tallies coming in from correspondents all over the country. The system then “tabulates the results and disseminates them in a number of formats to our member news organizations and customers.”
Sullivan cautions that he has no idea whether or not the “AP Vote Count” server is the same currently in-use “election night system” that the AP describes. “It seems quite possible that it is (but I hope I’m wrong),” Sullivan writes.
He clarified in an email, “But the greater point is this: AP uses something. If not these servers, then something. And given the state of those apvotecount servers… I’d say my concerns are quite valid that whatever is being used might not be as secure as it should be.”
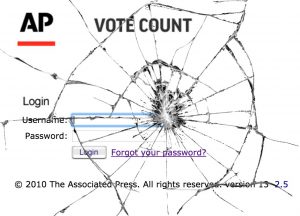
The login page for APVoteCount — still boasting a 2010 copyright — is, Sullivan notes, plain-text, not encrypted, and not protected by the more secure HTTPS protocol.
Neither does it appear to be safeguarded against a distributed denial of service (DDoS) attack. In a DDoS attack, a site is bombarded with so much fake traffic, generated from multiple sources, that it becomes overwhelmed and is forced to shut down. The outages of several major websites last Friday were due to DDoS attacks on the New Hampshire-based Domain Name System (DNS) service provider Dyn. (Mediaite was among the sites that temporarily went dark.)
One concern is that a hostile actor could bring down APVoteCount with a DDoS attack on the very night that countless news agencies are relying on it for up-to-the-minute results.
It’s important to note that an attack on the AP would not affect the official tallying of the election, which will be certified weeks after votes are cast. But chaotic reporting on election night could dissuade last-minute voters; it could also undermine confidence in the official results long after Nov. 8, especially in light of the allegations of conspiracy and fraud coming from the Republican camp.
According to a PRRI poll Tuesday, only 41% of Trump supporters had great confidence that their votes were going to be counted accurately (compared to 70% of Clinton supporters). According to a Reuters/Ipsos poll last Friday, nearly 70% of Republicans said they would attribute a Clinton win to a fraudulent election.
The AP has a longstanding policy not to comment publicly on its security measures and would not confirm whether or not the years-old server Sullivan discussed in his post was still in use. As recently as 2013, the New York Daily News cited — and posted screenshots from — something called “APVoteCount” when reporting on the results of the mayoral election.
An AP spokesperson would say only that the news agency “has been working diligently to ensure that vote counts will be gathered, vetted and delivered to our many customers on Nov. 8.”
Sullivan said, “Given the importance of a presidential election – a ‘no comment, because security’ just isn’t good enough.”
—
Sam Reisman (@thericeman) is a staff editor at Mediaite.
New: The Mediaite One-Sheet "Newsletter of Newsletters"
Your daily summary and analysis of what the many, many media newsletters are saying and reporting. Subscribe now!






Comments
↓ Scroll down for comments ↓